Home » Rants
The Evolution of the Windows BootkitDid you think Windows 7 was safe?
There's a strange meme circulating on the InterWebs. Namely that after being owned by the slings and arrows of outrageous hackerdom for the past twelve years, Microsoft Windows version Se7en is suddenly safe for Joe and Josephine Blogs to use. Where people got that idea is a mystery, although it's certain the PR departments at Microsoft have had a hand it.
Of course nothing could be further from the truth.
Eugene Rodionov, Aleksandr Matrosov, and David Harley put together a review and assessment of the status quo for Windows on behalf of their enterprise ESET. Again - and as will be pointed out time and again in this rant - there you have an IT corporation selling a product that's going to claim it protects an operating system that should have protected itself in the first place, and won't do a great job of it anyway.
Sucka.
http://blog.eset.com/2012/01/03/bootkit-threat-evolution-in-2011-2
And whilst some of that article and even this one may be over your heads, awareness of your own personal risks should never be. Further: readers are encouraged to do their own research - it's in your best interests.
Anyway: this article, as the report from ESET, has to do with wonderful developments in the World of Windows™ - with rootkits and bootkits. So on with the show.
Rootkits & Bootkits
The bootkit is the evolution of the rootkit. A rootkit is a malware software package that overtakes the entire operating system and hides from view, undetectable. It integrates into the system (such as Windows) and performs most of the stuff you'd expect the ordinary system to perform, whilst carrying on as well with its own nefarious agenda.
The advent of Microsoft's type of 64-bit programming was supposed to end all this. But of course Microsoft have been trumpeting the end of malware for over ten years, and what with their reluctance to actually change the architecture of the system itself (or replace it outright) there's no way any of these measures are actually going to help.
The AV industries play along with Microsoft of course: it's in their best interests that Microsoft Windows continues to be a vainglorious mess so they can keep selling their products. Of course none of these products really help much, but as long as you keep subscribing and paying them, they're happy enough.
Back to the bootkit. To work (im)properly, the bootkit has to get onto your system at a level below what the rootkit would normally use. Jimbo Wales can help explain.
http://en.wikipedia.org/wiki/Rootkit#bootkit
'A kernel-mode rootkit variant called a bootkit is used predominantly to attack full disk encryption systems... typically the malware loader persists through the transition to protected mode when the kernel has loaded.'
Now we already know Microsoft started using a 'trusted platform' model for their device drivers in Windows 7 so that stuff like this wouldn't happen - and more importantly so they could demand the manufacturers of peripheral media devices continually degrade quality, this to please the MPA and the RIAA who are terrified of file sharers and pirate production industries.
Not many people in the industry took Microsoft's security spiel seriously. The plebes kept buying the crap, but those in the know just shrugged and moved on. The malware pack Alureon penetrated the defences of Windows 7 back in August 2010. Alureon is a variant of the ever popular TDL.
http://www.prevx.com/blog/154/TDL-rootkit-x-goes-in-the-wild.html
http://www.theregister.co.uk/2010/11/16/tdl_rootkit_does_64_bit_windows
Back to ESET, for David Harley starts by first discussing TDL4.
'As we predicted in 2010, TDL4 (Win32/Olmarik) has been evolving over 2011. Its developers attempted to bypass the KB2506014 security update, which addressed a vulnerability allowing abuse of WinPE mode.'
Whoa. What's KB2506014? Microsoft aren't telling much but they do say this:
http://technet.microsoft.com/en-us/security/advisory/2506014
'Microsoft is announcing the availability of an update to winload.exe to address an issue in driver signing enforcement. While this is not an issue that would require a security update, this update addresses a method by which unsigned drivers could be loaded by winload.exe. This technique is often utilized by malware to stay resident on a system after the initial infection.'
So it's about an on-disk file, WINLOAD.EXE, with a bug.
'The issue affects, and the update is available for, x64-based editions of Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2. For more information about this release, see Microsoft Knowledge Base Article 2506014.'
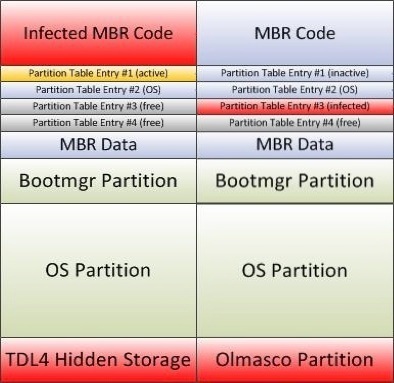
David Harley has a diagram of what a Windows disk looks like once it's been infected by one of these bootkits.
√ - Infected MBR code. MBR is your master boot record. Now and again you power off your computer or simply restart it. There's a basic bit of programming in there, coupled to the hardware, to get your system up and running. There's a small but important routine that takes charge of actually loading and running the code that's going to start your system. And that code is on your hard drive in what's known as the master boot record. Your computer is 'programmed' to find that area of your hard drive on startup or restart, to load what's there, and to then turn over control to the code there that it's just loaded.
That's your master boot record.
TDL4 will of course attack and infect this code, just as boot sector viruses did back in the nascent years of MS-DOS and Windows. What does this mean? It means that any system that starts up (or is restarted) will load the 'bad code' again. In a word: you're toast. You've been pwned.
√ - Partition table entries. Paraplegic Windows lets you create partitions on your computer's hard drive. These partitions get known as C:, D:, and so forth. Unlike mature operating systems, Microsoft's limits you to four such partitions. Their location on your hard drive is found in these partition table entries. The entries give the system the actual physical address (head, cylinder, sector) of each partition.
Some of these partitions might be 'bootable' - they might contain an operating system image. In which case you'll have an option on startup, which of them you want to run.
√ - TDL4 Hidden Storage. This is where the bootkit can hide its booty. It's very easy for TDL4 to do this - simply hide the disk area needed and then no system routine will think of going there. All this stuff is eminently easy on a Microsoft system - child's play.
What David Harley never explains of course is how the bad code got to overwrite the master boot record in the first place. For the interesting thing isn't how the danged thing works, but why Microsoft sold you a product that wasn't designed to stop this from happening.
Perhaps Harley and his buds don't think things like that are important. Anybody can corrupt anything on a Microsoft system at any time. That's the general rule. But master boot records reside on hard drives, and hard drives are supposed to be off-limits to user code. You can't do something that outrageous on a Unix system.
Olmasco
A new bootkit appeared in the wild in 2011. Olmasco. It's based on TDL4. But Olmasco doesn't corrupt the MBR - it corrupts the partition table and allocates disk space for its own nasty partition. See the diagram above.
ZeroAccess
Another new bootkit appeared in 2011: ZeroAccess. This one doesn't infect master boot records and it doesn't infect partition tables either.
ZeroAccess works both on older 32-bit systems and newer 64-bit systems. On 32-bit systems, ZeroAccess overwrites the kernel mode boot start driver with its own code - something Microsoft evidently are quite OK with - and sets up hooks in the storage device driver stack to avoid detection by 'security kits'. Again, it's wide open to do stuff like this on Windows.
ZeroAccess doesn't have a kernel mode driver for 64-bit as those other bootkits do, but instead drops off the lovely CONSRV.DLL into the 'System32' directory - just like that. This directory is supposed to be protected by Microsoft. User code isn't supposed to be able to get in there. Such a thing is certainly not possible on a mature system like Unix. But with Microsoft running the show for Windows, there doesn't seem to be murmur of protest. What's up with that?
CONSRV.DLL
So ZeroAccess drops off CONSRV.DLL into a protected area where no self-respecting system would let anyone tread, then it registers itself as part of the 'Windows subsystem', something that again should be off-limits, and that's done so the bootkit ZeroAccess can screw up Microsoft's session manager subsystem module SMSS.EXE the next time it runs - it's all stored in the Windows Registry at a location that's supposed to be protected from tampering (except it's not).
HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\SubSystems
Some Registry paths (the Registry's patterned like a file system) are supposed to be off-limits (owned by the system itself) and can even be undetectable to the user on occasion. But not here. Not now. All those wonderful assurances from Microsoft could still apply, but your friend ZeroAccess got in anyhow.
But it gets worse still: for by putting its own file CONSRV.DLL in the subsystem list, and because Windows won't start up if there's a file in that subsystem list it can't find, then removing the file CONSRV.DLL without removing the Registry entry ends up hosing the entire Windows system and renderings it unusable. Isn't that great?
Stop for a second and review what you've seen so far.
- TDL4 and Olmasco can magically write directly to the computer hard drive.
- ZeroAccess can write to the system area 'System32', overwrite the boot start driver, and write to a supposedly protected Registry area.
Keep that in mind. Now moving on.
Rovnix
Rovnix is another newcomer for 2011. This one uses yet another technique: it modifies partition sector (VBR) code and bootstrap code both. This is good for Rovnix, as it makes it easier still for malware in general to run rings around antivirus products, but it's not good for you. Code like Rovnix can be purchased online.
Sophistication
Bootkits are increasingly sophisticated, all the while Microsoft Windows 7 remains a sitting duck in terms of security, failing the most elementary tests and letting users suffer financial losses in the hundreds of millions annually.
The mere creepiness of the idea that someone is inside your computer, spying on you, plotting to gut your savings accounts, steal your identity, your credit cards, and Microsoft sold you such a useless system without so much as a blink - that's enough to make almost anyone taste their dinner twice.
Bootkits are starting to use their own system routines that they store in hidden areas of your hard drive. As the hidden areas are not likely to be detected by antivirus software, the bootkits themselves will even more easily escape detection.
David Harley goes on in his article to compare the types of hidden storage used by this new generation of rootkits (the bootkits) but that's not germane to the topic at hand, which actually is the following.
√ How can code that is run directly or indirectly by any system user at all in the year 2011 (2012) get direct access to the computer hard drive? This is off limits. This is impossible on all mature systems. The hard drive is a shared resource. Its only access path is through the OS kernel and thereafter through the device driver that interfaces with the actual physical hardware. Getting this low requires privileges the ordinary user (you) isn't ever supposed to have. Where has the Microsoft security model gone on holiday? For how long?
√ How can user code modify anything in 'System32'? It's the same anomaly as above. How can use code modify protected areas of the system Registry? It's the same thing again.
The issues at hand for ordinary (Windows) users have nothing to do with the details of these nasty bootkits. What ordinary users want to know is how that stuff gets on their systems in the first place.
David Harley and his friends at ESET don't seem to think that's pertinent. Most likely because Windows is the wide open system they all know it to be. And for bootkits like TDL4, Olmasco, and ZeroAccess to proliferate, they need an attack vector (means of attack) they can rely on, no matter whose computer they're after. An attack vector all Windows computers have in common.
Yet what this magical common denominator is - it's never mentioned. It seems likely it's the same as it's always been - the overall lack of a good security system at Microsoft.
The very spectre of Microsoft spending billions upon billions trying to defend such a ridiculous system with such shallow shadow games... All that great and vainglorious code, and the system at its most fundamental level is still such a mess that the security gurus don't even bother worrying about how the bad stuff gets on your computer in the first place... Because it's going to get on there no matter what, whether or not you or Microsoft want it there...
Talk to friends who run Unix systems and know what they're doing. At the very least ask them if they invest in antivirus software, if they've ever been attacked by bootkits, or rootkits, or other malware. Do the research - not so you immediately go out and buy a new computer, but so you begin to realise what a sucker Microsoft played you for.
|